a.
Batch - A batch operating system is one of the earlier OS systems and concepts developed. It was actually assigned to take or perform tasks from a Job pool or Batch of jobs, also now known as batch jobs. The batch operating system may not exist but certainly it isn't extinct because no OS today perform without having batch jobs being a part of it. Batch jobs nowadays are a fundamental part of modern OS and working principle.
b.
Time sharing - it was an operating system for RCA (
Radio Corporation of America)
mainframes of the
RCA Spectra 70 series.RCA was in the computer business until 1971. Then it was sold to
Sperry Corporation; Sperry offered TSOS renaming it to
VS/9. In the mid seventies, an enhanced version of TSOS was offered by the German company
Siemens and was called
BS2000 here.While Sperry (respectively Univac after the company was renamed) discontinued VS/9 in the early 80's, BS2000, now called BS2000/OSD is still offered by
Fujitsu Siemens Computers and used on their mainframe customers primarily in Europe.TSOS was the first operating system that supported virtual addressing of the main storage. Beyond that it provided a unique user interface for both, time sharing and batch which was a big advantage over
IBM's
OS/360 or their successors
MVS,
OS/390 and
z/OS as it simplified the operation.
c.
Real time - A Real-Time Operating System (RTOS) is a
multitasking operating system intended for
real-time applications. Such applications include
embedded systems (programmable thermostats, household appliance controllers), industrial
robots, spacecraft, industrial control (see
SCADA), and scientific research equipment.A RTOS facilitates the creation of a real-time system, but does not guarantee the final result will be real-time; this requires correct development of the software. An RTOS does not necessarily have high
throughput; rather, an RTOS provides facilities which, if used properly, guarantee deadlines can be met generally or deterministically (known as
soft or hard real-time, respectively). An RTOS will typically use specialized scheduling algorithms in order to provide the real-time developer with the tools necessary to produce deterministic behavior in the final system. An RTOS is valued more for how quickly and/or predictably it can respond to a particular event than for the amount of work it can perform over a given period of time. Key factors in an RTOS are therefore a minimal
interrupt latency and a minimal
thread switching latency.An early example of a large-scale real-time operating system was
Transaction Processing Facility developed by
American Airlines and
IBM for the
Sabre Airline Reservations System.
d.
Network - A network operating system (NOS) is
software that controls a
network and its
message (e.g.
packet)
traffic and
queues, controls access by multiple users to network resources such as files, and provides for certain administrative functions, including
security.The upper 5 layers of the
OSI Reference Model provide the foundation upon which many network operating systems are basede.
e.
Distributed - Distributed operating systems have many aspects in common with centralized ones, but they also differ in certain ways. This paper is intended as an introduction to distributed operating systems, and especially to current university research about them. After a discussion of what constitutes a distributed operating system and how it is distinguished from a computer network, various key design issues are discussed. Then several examples of current research projects are examined in some detail, namely, the Cambridge Distributed Computing System, Amoeba, V, and Eden.
f.
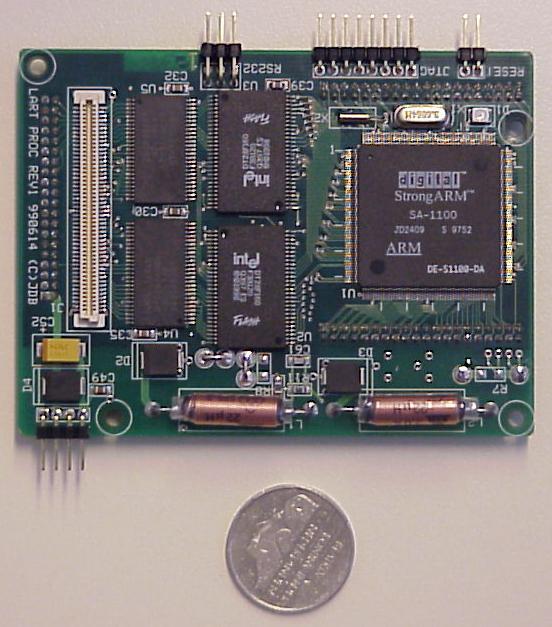
handheld - A handheld PC's operating system determines not only what you see onscreen, but also how you interact with the device and what kind of services you can get from it. The two dominant handheld OSes are Palm and Pocket PC but Symbian and Linux are both up and coming. To help you decide which OS you want on your next handheld, here's a breakdown of these four operating systems plus a few of our hardware picks to get you started.